12 Tools to Verify File Integrity Using MD5 and SHA1 Hashes
TL;DR
When downloading files, it’s crucial to check their integrity to ensure they haven’t been altered or infected. You can do this by verifying the file’s digital signature or calculating its hash value. Popular tools like ManageEngine, SolarWinds, and HashMyFiles can help you check file hashes for security.
Why do you need a file verification tool?
Downloading files from the internet always carries a risk of them being altered—whether due to corruption during the download process or tampering with malicious intent. Checking a file’s hash value is an effective way to verify its integrity and ensure it matches the original.
Read more:
- Cheapest Code Signing Certificate and Walkthrough in Getting It
- Links for Windows 7 SP1 ISO from Microsoft’s Official Distributor
What Is a File Hash?
A file hash is a unique string generated from a file’s contents using a cryptographic hash function. It’s used to verify that the file hasn’t been altered. Even a single byte change will produce a different hash value. Common hash algorithms include MD5, SHA-1, and SHA-256.
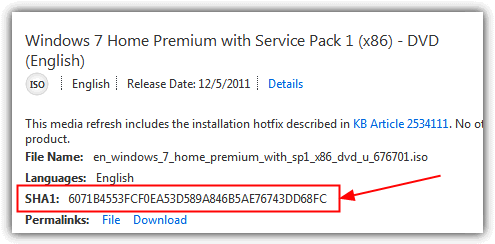
How to Check File Integrity
If you have a hash value from a trusted source, you can compare it to the hash of the file you downloaded. Many tools can help you calculate and compare hash values. Below are 12 of the best options, tested on Windows 7 and 10.
Best File Hash Checkers
1. ManageEngine
ManageEngine is a file integrity monitoring application that lets users keep track of file changes in real-time. With this application, users can track unauthorized changes to critical files, monitor suspicious edit patterns, and evaluate file permission changes. They can also create templates and filters to oversee specific groups of files on as many devices as they need. The software integrates CASB and DLP features and provides a powerful FIM module that helps users meet compliance and security standards.
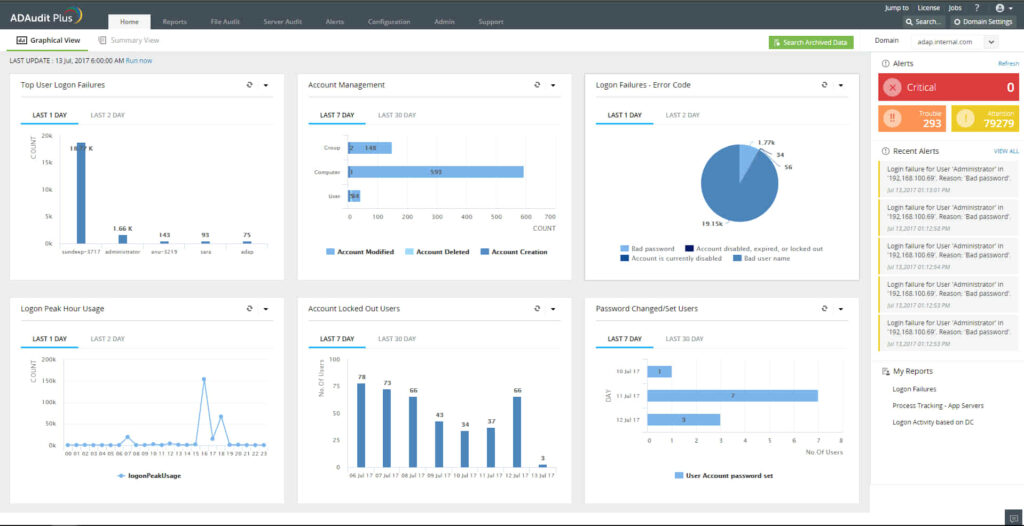
ManageEngine uses both agent and agentless methods, allowing the business’ security team to choose their implementation method based on the company’s requirements. Furthermore, the software thoroughly audits the file and folder activities before delivering a full report on the risks to the document is exposed to. The software also generates in-depth reports to track file access, modification, deletion, permission change, and creation. Users can create warning alerts based on event patterns, time frame, or count. These alerts are delivered via email or SMS when there is unauthorized access.
Additionally, the application has a user-friendly interface that doesn’t require much technical knowledge before set-up. The app also automatically updates audit policies, SACL settings, and agent updates.
2. SolarWinds
This popular file integrity checker allows users to keep track of file modifications. Formerly known as Log & Event Manager, this application provides a central log record of all changes made to the file hashes. The software has an in-built surveillance feature that tracks unauthorized access to executable files, logs, configurations, databases, and more.
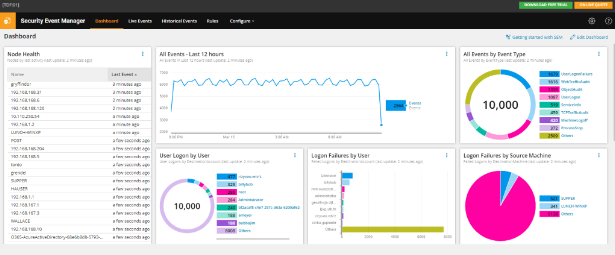
The SolarWinds Server and Application Monitor provides an added layer of security as it comes stock with over 1,000 application monitoring templates. With this tool, users can monitor file changes across public, private, or hybrid conditions. The business is also able to track user activity before and after file modification exercises.
3. IgorWare Hasher
Hasher is a small, portable and easy to use freeware tool that is able to calculate SHA1, MD5 and CRC32 checksums for a single file. You can browse for the file, drag and drop or add a context menu entry to right click and choose “Generate Hash”. There’s also an option to generate a hash from a block of text which you can type or paste into the box. The program opens a window for each file you select so don’t open more than a couple at once.
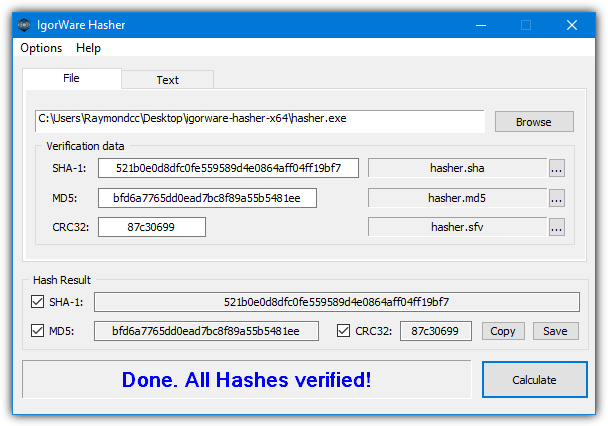
In addition to copying or saving the hash result to a file, you can load the hash file back into the program to check against another or the same file. The Options menu has some useful settings like keeping the program on top, making the hash values upper case, auto calculating after drag and drop, and adding the context menu entry. For some strange reason, Igorware Hasher downloads as a RAR file so make sure you have an archiver like WinRAR or 7-Zip to open it.
4. HashCheck
HashCheck works in a slightly different way to a traditional checking tool because it integrates into the system’s file properties window. You’ll get an extra tab called Checksums alongside the standard tabs of Compatibility, Details, Previous versions and etc. The original Hashcheck is from 2009 but seems to work fine in Windows 10. A more recent version is available on GitHub which we’ll also mention below.
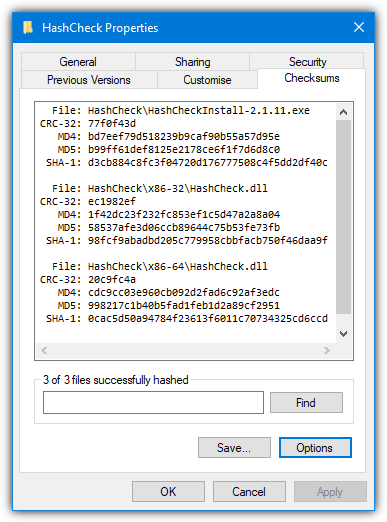
The tiny (85KB) installer simply registers HashCheck.dll on the system so it’s very light on resources. Right click on one or more files or a folder and go to Properties > Checksums. Values for CRC-32, MD4, MD5, and SHA-1 will be shown in the window. The Save button can save the selected file checksums into a separate list for each hashing method which you can load later on to see if any of the files have changed.
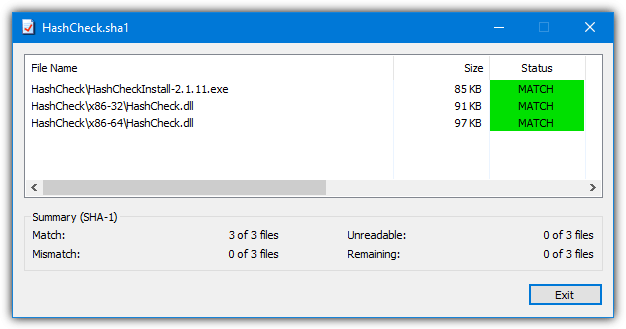
A list can be created quickly from the context menu by right clicking on the file(s) and selecting “Create checksum file”.
As HashCheck is open source software, someone has taken the original code and updated it while adding some new features. Notable improvements include multithreading support, adding SHA-256 and SHA-512 (MD4 has been removed), calculating only selected checksums, adding extra translations, and digitally signing the files/installer.
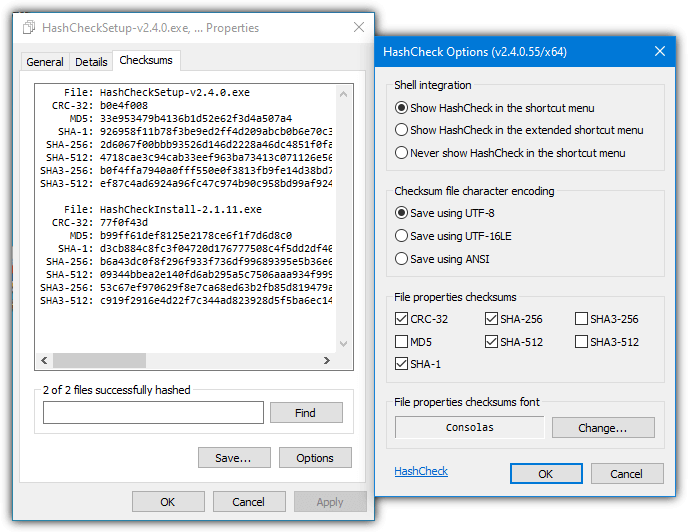
This version of HashCheck is much newer and from 2016. It was created by Christopher Gurnee and is hosted on GitHub. MD5 and SHA-3 are disabled by default in this version but can easily be enabled in the Options window.
Download HashCheck 2.4 From GitHub
5. Nirsoft HashMyFiles
HashMyFiles is another small and portable tool from Nir Sofer that is simple and straightforward to use. The number of ways to open files is impressive because you can add single or multiple files, folders (including sub folders), running processes, and also by wildcard with custom folder depth. There’s also the Explorer context menu which can be manually enabled. The program shows hashes for CRC32, MD5, SHA-1, SHA-256, SHA-384, and SHA-512. General file information is also included in the display.
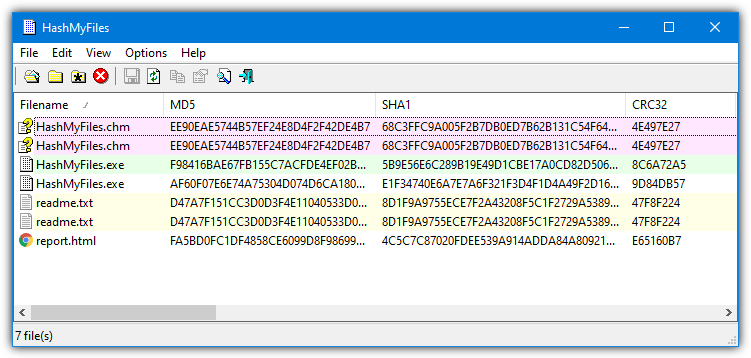
HashMyFiles can export the data to a TXT, HTML, XML or CSV file but you can’t use it to load back into the program to re-check files later on. A number of command line arguments are also available and other functions like always on top, extra file information, uppercase text, and send the hash to VirusTotal are in the Options menu. Also in the Options menu, “Mark Hash in Clipboard” compares a hash in the clipboard with the files and will show a match in green. “Mark Identical Hashes” shows the same files in differing colors.
6. HashTools
HashTools is from software developer BinaryFortress who make well known shareware applications like DisplayFusion and ClipboardFusion. This program is portable and will accept an individual file, multiple files or an entire folder for processing. An option to add a “Hash with HashTools” entry to the context menu is in the Settings window.
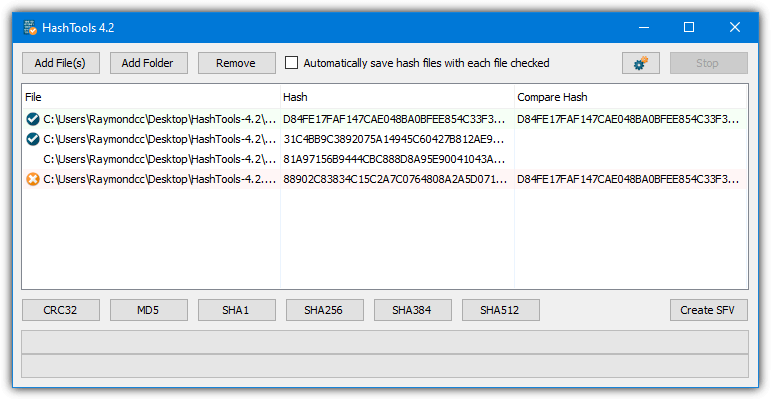
When you add files to HashTools they will not be processed until you press one of the buttons across the bottom to calculate the appropriate checksums. CRC32, MD5, SHA-1, SHA-256, SHA-384, and SHA-512 are supported. The Create SFV button will create CRC32 checksums for the files and save them into an SFV file which you can use to verify later on. Right clicking a file will allow copying of the hash or its path along with supplying a hash manually or from the clipboard to compare with.
7. ComputeHash 2.0
ComputeHash is a small and very simple tool to use with no advanced or confusing features. It works entirely from the Windows context menu and you simply right click on a file and select the “Computer Hash” option. It will display MD5, SHA-1, SHA-256, SHA-384, and SHA-512 hashes all at once. Double click the executable to add the entry to the context menu, use uninstall.bat to remove it again.
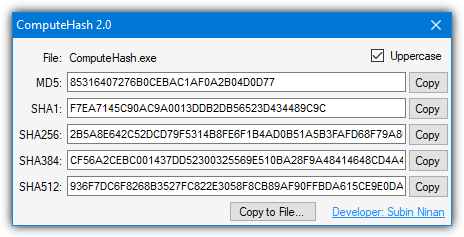
Each checksum can be copied to the clipboard, or all values can be saved to a text file. The uppercase checkbox might make the values a bit easier to read. ComputeHash requires .Net Framework 2 so Windows 10 users will be prompted to install it if it’s not already installed. We are looking at version 2.0 from 2011 here, there is a version 4.4 from 2015 but we found it doesn’t display the checksums properly in Windows 7 or Windows 10.
8. MultiHasher
This utility is by the same developer as the well known HostsMan Windows HOSTS file editor. It has a number of useful options and files can be added to the list in several ways. You can open one or multiple files at once, entire folders (including sub folders), by paths, by running processes and via nine different types of hash list. It can also create a hash value for small text strings. CRC32, MD5, RIPEMD and the SHA family of hash algorithms are supported.
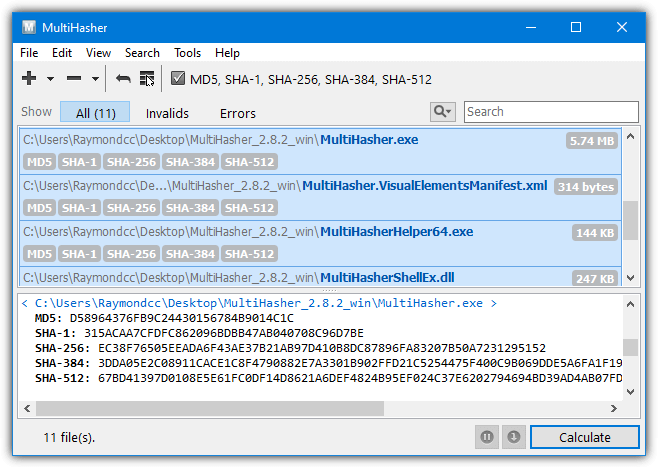
File association, drag and drop and the right click context menu option is also there, along with an option to search for the checksum on Google. A potentially valuable feature for those that need it is the ability to upload and query files on Virustotal. This requires an API key from VirusTotal but anyone can get a key by signing up for a free account. Uploading and checking can then be done from within MultiHasher. Portable and installer versions of MultiHasher are available.
9. 7-Zip
7-Zip is probably the most popular and well known free file archiver around today. Not least because of its 7z archive format that can achieve great compression ratios. The ability to verify file checksums with CRC or SHA has been in 7-Zip since 2011. A few years later a function was added to 7-Zip that introduced a context menu entry where you can quickly check a file’s integrity through the program’s user interface.
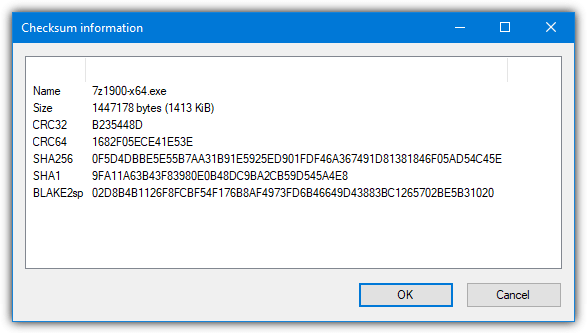
Just right click on a file and go to “CRC SHA” and the options will be available to get a checksum for CRC-32, CRC-64, SHA1, SHA256, or the asterisk will get all at once (including BLAKE2sp). Do note that when you select multiple files 7-Zip will give the overall checksums for all files added together and not each file individually. The 7z.exe command line tool has this function by using the “h” command along with a hash switch “-scrc[CRC32|CRC64|SHA1|SHA256|*].
7z.exe h -scrcSHA256 [filetocheck.ext]
10. HashTab
HashTab is another tool that uses the system file properties window to show file hashes and is quite similar to HashCheck. After right clicking on the file and going to Properties, the tab is called “File Hashes” and you will get CRC32, MD5 and SHA-1 hash values displayed by default. One major limitation HashTab has compared to HashCheck is it only works on one file at a time.
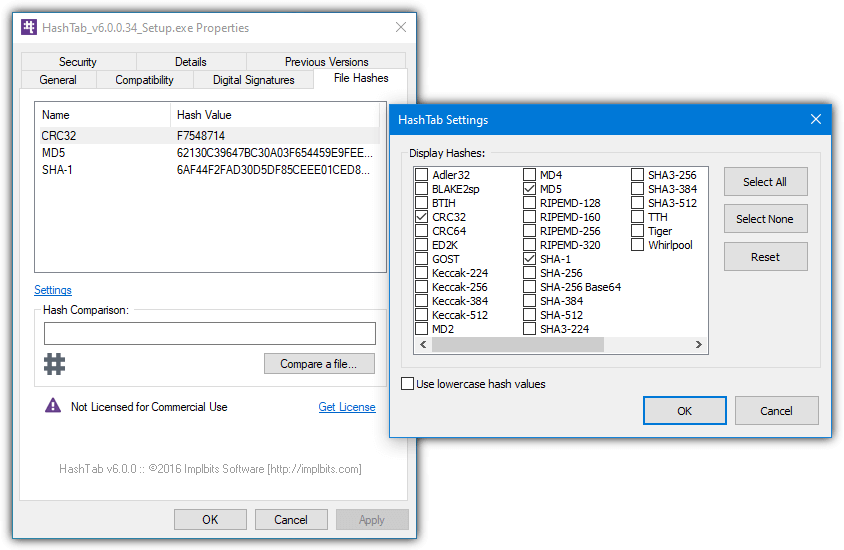
Pressing Settings gives access to an impressive selection of 27 additional hash values that can all be displayed. These include the Keccak, RIPEMD, SHA and MD families along with several others like GOST, ED2K, Adler32, and Tiger. You can compare the current file with a hash value in the clipboard by using the Hash Comparison box or use the “Compare a file” button to compare another file with the selected one.
11. Hasher
Not to be confused with the Igorware tool at the top of our list, this hashing tool is pretty simple to use and lets you drag and drop or browse for a single file to get a checksum. We are looking at version 1.20 from 2009 as all the later versions have a five second nag window on startup, so we really can’t recommend them. They do have more available hashes and folder/multi-file support if you feel like trying one out.
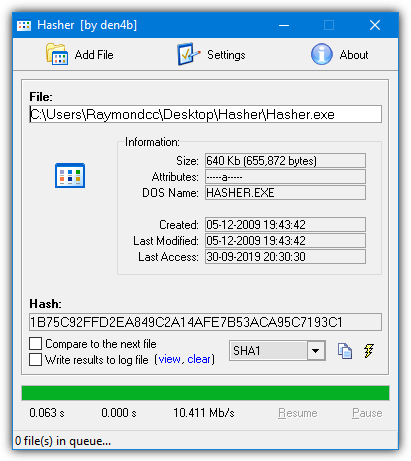
This older version is a small executable and will give you hash values for CRC32, MD5, SHA-1, and ELF. The current hash can be copied to the clipboard and you can manually compare the current hash value with a previous one from the clipboard or the next file that gets checked. Enabling the log file will keep a history of processed hashes and any comparison results.
Download Hasher (version 1.20 is at the bottom)
12. Microsoft CertUtil, FCIV, and PowerShell
We’ve grouped these three options together as they are all by Microsoft and the first two are built into Windows. They can be useful for adding into scripts or creating simple drag and drop shortcuts and etc.
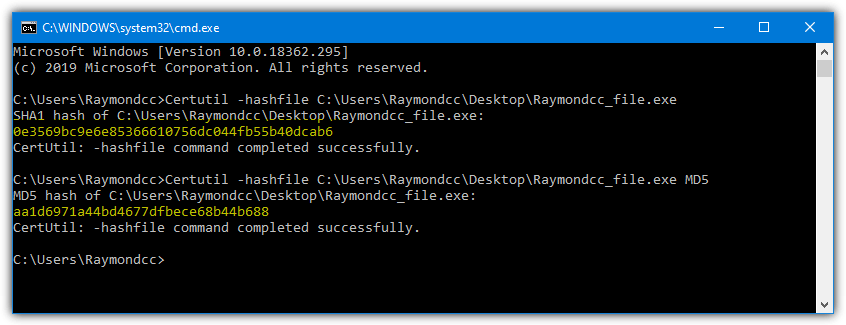
Certutil
CertUtil is a command line tool that is primarily for showing information for and handling digital certificates on the system. One of its functions is being able to show the hash of a file, which is what we are looking for. The command to use for a file is as follows.
Certutil -hashfile [filetocheck.ext]
This will output the SHA1 checksum of the file. Other algorithms are supported, just append MD2, MD4, MD5, SHA256, SHA384, or SHA512 to the line and it will show that value instead. Only one algorithm is supported at a time, so if you want SHA1 and MD5 you will have to run the tool twice.
Certutil -hashfile [filetocheck.ext] MD5
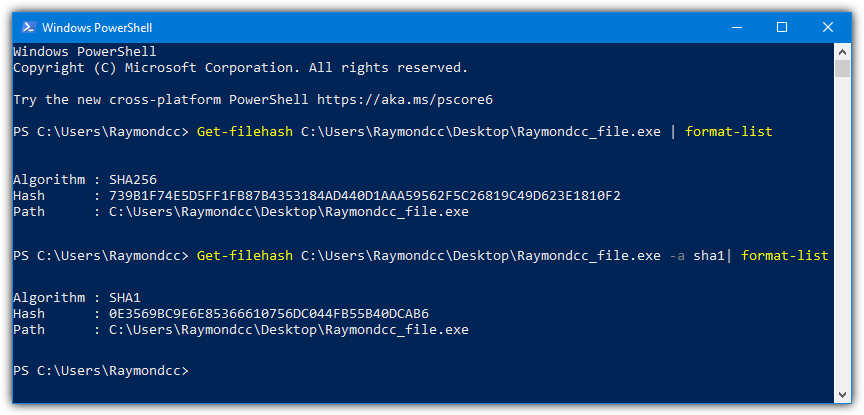
PowerShell
The PowerShell function is also built into Windows so needs no external executable. It works in a similar way to CertUtil. Windows 7 users will need to manually install PowerShell version 4 or above for this command to work.
Get-Filehash [filetocheck.ext]
Just supplying the file to the get-filehash command will output the hash as SHA256 by default. You can change this by adding -a and the new algorithm, MD5, SHA1, SHA384, SHA512, MACTripleDES, and RIPEMD160 are supported.
Get-Filehash [filetocheck.ext] -a SHA1
Note that like the Certutil tool, only one hashing method can be entered into the command at a time.
FCIV
This last tool is not built into Windows but is still made by Microsoft. The File Checksum Integrity Verifier (FCIV) is from way back in 2004 and Microsoft offers no support for it. It has a few more advanced options than the other two commands, including recursing into subdirectories, an exclusions list and the ability to save/list/verify checksums in an XML database.
Fciv [filetocheck.ext]
By default, FCIV outputs MD5 checksums but you can change this to SHA1 by appending -SHA1 or -Both to output MD5 and SHA1 at the same time.
Fciv [filetocheck.ext] -Both
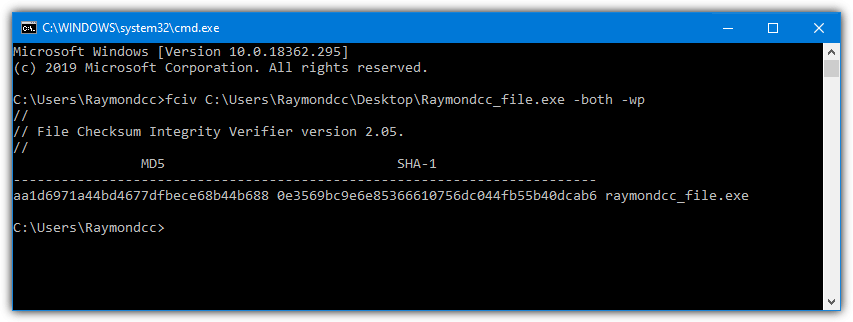
It’s odd this tool has no support because it has a proper knowledge base designation of KB841290 and there is a full page on the Microsoft website detailing FCIV’s usage. A download link is on the same page.
Download Microsoft File Checksum Integrity Verifier
There are dozens of these tools about, and you might already have your favorite. Of course, feel free to tell us about the hash program you like best. If you want to try the reverse and actually have a go at identifying the file from a hash value, you might like to look at this article.
Wrapping up
In conclusion, verifying file integrity is essential for ensuring the authenticity and security of your downloads.
You can also explore other helpful tools like how to create an up-to-date Windows 7 installation disc or download an official Windows 7 ISO from Microsoft’s distributor. These articles will guide you in verifying and securing your files with ease.



User forum
45 messages